SPF Limit.
No, we’re not discussing the Sun Protection Factor recommendation of at least 30.
While such SPF is truly important to protect your skin from damage, this article isn’t about a sun defense mechanism at all.
Instead, we’ll discuss the email authentication mechanism kind of SPF that catches forged senders during email delivery.
More particularly, we’re talking about the Sender Policy Framework limitations.
These are constraints to the SPF system, which filters out spammers from phishing, spoofing, and spamming email users. Still trying to understand the email technicalities?
Don’t worry. It’s not as difficult as you think.
Keep reading to learn about SPF authentication limitations, how SPF records work, whether SPF limitations are necessary, and more! We hope you’ll walk away as a more informed email marketer by the end of this article.
But to help you see the bigger picture, it’s better to have a deep understanding of what the Sender Policy Framework (SPF) is.
![]()
What is SPF?
Have you ever received a nonsense email that appears to be from Microsoft but, in reality, from a spammer impersonating Microsoft? That’s an example of a “spoof” email.
Spammers do this by faking the domain linked with a legitimate email (in this example, Microsoft). In spoofing attacks, spammers usually forge email headers or display the sender’s address.
This is where SPF comes in the story. It is created to combat spoofing.
Sender Policy Framework is an email authentication mechanism designed to:
- Improve domain reputation – It improves the domain reputation with email clients and Internet Service Providers (ISPs), increasing the chance of emails landing in the inbox.
A domain is the full name of an email (or a website). An example of a domain name is “cloudfare.com.” While a personal email account may use “@yahoo.com” or “@gmail.com” as its domain, a business will use the company’s website.
- Enhance email deliverability – It does so by reducing the chance of emails being marked as spam.
- Combat email spoofing and phishing – The SPF record verifies the sender’s IP address. It protects the domain from spoofing, lessening the likelihood of domain blacklisting.
- Support compliance – The SPF assures compliance for industries where emails are regulated by confirming the legitimacy of said communications.
- Fight phishing attacks – It prevents malicious actors from sending phishing emails that seem to come from your domain.
How Does SPF Work?
It’s a simple technical process once you understand the basics, as we shared above.
During mail delivery, it enables the recipient mail server to verify that a message claiming to come from a certain domain is indeed sent from an IP address allowed by the domain’s administrators.
Once the receiving server verifies that the domain’s owner authorized the incoming email, it will accept such email. On the other hand, if it fails, the email will be rejected or considered as spam.
Hackers and spammers may impersonate a legitimate domain and send campaigns that look like they’re coming from a legitimate source.
Imagine this: When people receive a spoofed message, they’ll be annoyed and put the email in the spam. Ultimately, this can have a negative impact on the overall domain reputation and email security of the legitimate domain owner.
Why Do You Need SPF Records?
An SPF record is a type of DNS record (a.k.a. zone file) that lists servers authorized to send emails from a domain or on behalf of an institution.
SPF records are important to email security. It assists in preventing phishing and spoofing scams by confirming that the IP address sending the email is legitimate and linked to the domain.
Having correctly configured SPF records also improves domain reputation and deliverability.
Example Of SPF Record
Here’s an example of an SPF record uploaded to DNS for processing.
v=spf1 ip4:192.0.2.0 ip4:192.0.2.1 include:examplesender.email -all
Let’s understand better each element of the above SPF record format.
– v=spf1 .This string instructs the server that it contains an SPF record.
– ip4:192.0.2.0 ip4:192.0.2.1. This is the “guest list” part of the SPF record. It indicates the list of authorized IP addresses to send on behalf of the domain.
– include:examplesender.email. This tag indicates that the provided domain (examplesender.net) should be examined, and the IP addresses contained within it should be authorized.
–all. Finally, this signals the server that addresses not included in this SPF record should be rejected and is not authorized to send emails.
The SPF record is published in the DNS that you’ll see in your domain host provider. Once you log in to your domain account, there’s a page for updating DNS records. It is something like name server management or DNS management.
To learn more about how to set up an SPF record, check out this in-depth guide – DKIM vs SPF – What’s The Difference?
Now, what are SPF Limitations?
A Closer Look at the Sender Policy Framework (SPF) Limitations
SPF specification has a total of 10 DNS SPF lookups limit per SPF record.
If you exceed the 10 DNS lookup limit, your SPF record check will fail. This applies to you if you own a domain and want to add an SPF record to the DNS database.
What Happens if You Exceed Ten DNS Lookups?
You’ll get the ‘SPF too many DNS lookups’ error. The email is then returned or the list of approved IP addresses is not retrieved.
Additionally, the receiving email system will reject the SPF validation with an error (called permerror). This increases the chance for adversaries and hackers to use your domain to send spoof emails.
Moreover, if the DNS PTR query (pointer record reverse- DNS lookup) provides more than 10 results, it will only use the first 10 results. Take note that the use of the SPF PTR mechanism is discouraged.
Are the Sender Policy Framework (SPF) Limitations Necessary?
Yes, the SPF DNS lookup limit reduces the usage of the resources (CPU, memory, time, and bandwidth) that email service providers spend. They lessen the burden on their servers.
The standard 10 SPF lookup limit also protects the receiving mail servers from a Denial-of-Service (DoS) attack. DoS is meant to shut down a network or machine, depriving legitimate users (i.e., account holders, members, or employees) of the service they expected.
Why Does SPF Lookup Failure Happen?
1. People Forget Their SPF Limit
One of the significant reasons why SPF lookup failure happens is many people forget about the SPF limit.
2. Users Fail to Check Their Logs
Email marketers test and validate their SPF records for syntax typos and errors but sometimes fail to check the logs in their SPF lookup counter.
Each mechanism added in the SPF record, such as a redirect, exists, ptr, include, and MX, will be counted as one DNS lookup entry.
3. Lookups Quickly Add Up
Another reason is these lookups quickly add up.
Google, for instance, requires its customers to include SPF record _spf.google.com in their respective domain SPF records.
However, upon looking at the contents of the records in DNS, users may discover that it contains three Google.com subdomains.
In this scenario, such a Google customer will already have four lookups: one for the SPF record _spf.google.com and three for the Google subdomains.
Imagine if you include the SPF records of other email service providers, which may have different DNS lookups.
4. Use of Third-Party Senders
Many companies now use third-party senders, either through an intermediary service or sent by someone else on behalf of the business.
Unfortunately, these third-party senders take up three or four servers that enable you to max out the 10-lookup limit quickly.
For instance, your firm uses Workday, Zendesk, and Google Apps for Business. These cloud services can send mail on your behalf, meaning adding the corresponding SPF records for these platforms.
Each of those records, though, may have multiple SPF lookups on their own.
5. The Receiver Stops Evaluating the Record
Remember when we highlighted earlier how the SPF enables a domain to determine which servers may send emails on its behalf?
SPF records comprise a set of rules that are evaluated sequentially (from left to right) based on the parameters. For instance, v=spf1 indicates the beginning of the rule and what SPF version to be used. [See Example Of SPF Record for recall].
A message can be validated by the rule that was set early in the SPF record and will be authenticated despite having a broken SPF record.
Those messages that appear later in the SPF record and are meant to be authenticated by the rules can fail. It happens because the receiver stops evaluating the record before ever reaching the rules.
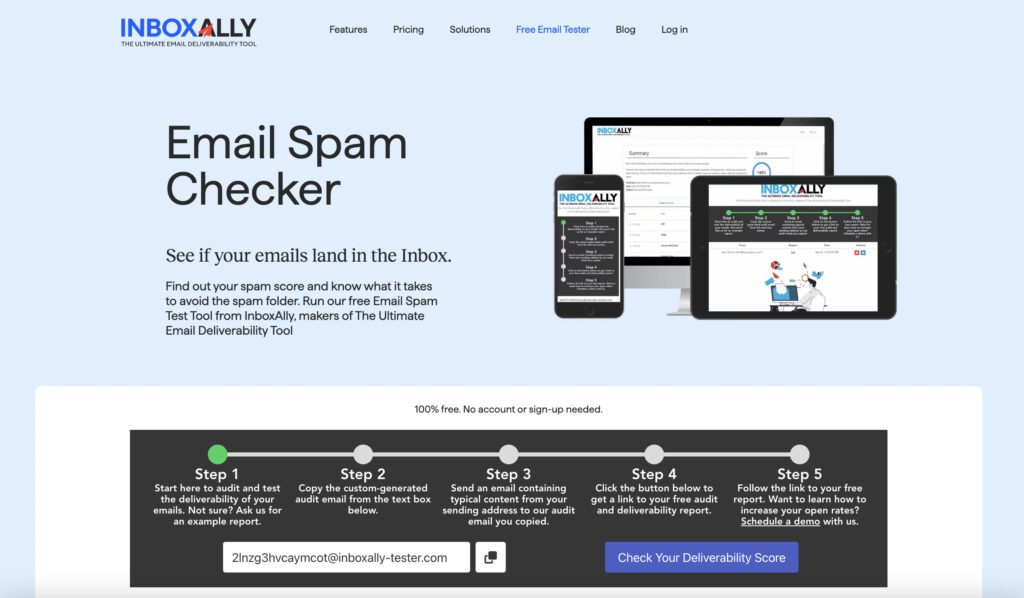
If you’d like to learn more about email authentication to maximize return on your investment, check out InboxAlly. It’s the ultimate deliverability tool that helps you stay in the Inbox. Get in touch with our team.
The Way Out
Fortunately, there are ways out of SPF DNS lookup failure.
Solution 1: SPF Record Flattening
This is one simple solution where you compress the information of multiple SPF records into a long one. By “flattening” the SPF record, you’re staying in the “safe zone.”
It also works by replacing the original modifier/ mechanism with IP addresses. So, each time a modifier or mechanism is replaced, the lookup count is decremented by one.
Solution 2: Remove the Default SPF Values
Many hosting services have a default SPF policy each time a new domain is added. To prevent SPF DNS lookup failure, check the DNS records because there may be mechanisms that are not needed.
SPF can improve an organization’s email security but is not self-sufficient.
To be more effective, it should be part of a multi-layered email security approach with DMARC (Domain-based Message Authentication, Reporting & Conformance) and DKIM (Domain Keys Identified Mail).
Learn more about these email authentication protocols in this post: SPF, DKIM, DMARC explained [Infographic]
How InboxAlly Can Help
If your concern is to strengthen your campaigns’ email security posture, try InboxAlly. It’s the ultimate deliverability tool that can repair or increase deliverability on any IP or domain on any platform.
In fact, there are so many things that make the tool famous among email marketers, list owners, deliverability experts, agencies, and email service providers.
You can rely on it for all things email – from working with any email-sending service to allowing users to create multiple sender profiles to accommodate all their domains/ IPs.
InboxAlly also teaches email providers to put their messages in the Inbox right from the start and track the progress of their campaign. In the dashboard, you’ll see where your emails have been landing in the last 30 days.
To Wrap It Up
Thank you for reading till the end.
You may already know by now that the Sender Policy Framework record can improve your email deliverability and protect your domain reputation. It isn’t perfect without other email authentication methods, but it’s a simple yet elegant solution.
Here’s the thing, though: the SPF implementations limit the number of lookups to 10 per SPF check. If you’re worried about this happening, use the tips we shared above to overcome these SPF limitations.
Want to protect your domains from phishing and spoofing attacks without worrying about email authentication? Try InboxAlly for free. It’s a unique email deliverability tool that can improve your sender reputation with inbox providers and optimize your campaigns.
Don’t forget to check out our blog for more email marketing insights.